Technology
How to Enhance Image Quality Without Advanced Editing Skills
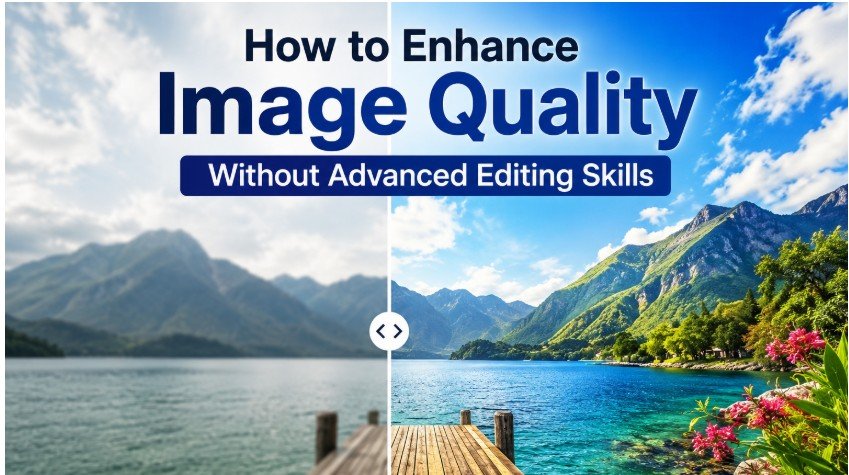
Good images matter more than ever. Whether you post on social media, sell products online, or share personal memories, clear and sharp photos make a strong first impression.
The good news is that you no longer need to be a professional photographer or designer to improve your photos. AI-powered tools now make it easy to enhance photo quality in just a few steps, even if you have zero editing experience.
Part 1. Understanding Image Enhancement
Image enhancement means improving the technical quality of a photo. It is different from creative editing. Enhancement focuses on fixing real problems, such as:
- Blurry or out-of-focus images
- Low-resolution photos with visible pixelation
- Noise, grain, or unwanted artifacts
- Dull colors, weak lighting, or poor contrast
Editing vs. Enhancement
Editing is about creative changes. You add filters, effects, or artistic styles. Enhancement, on the other hand, is about restoring and improving what is already there. Both serve different purposes, but enhancement is what you need when a photo looks unclear or low quality.
Traditional Editing vs. AI Enhancement
Traditional manual editing takes time and skill. You need to learn tools, adjust settings manually, and repeat the process for each photo. AI enhancement is different. It reads the image automatically and applies the right corrections in seconds. The results are fast, consistent, and require very little effort from you.
Part 2. Why Adobe Photoshop Can Be Difficult for Beginners
Photoshop is a powerful tool used by professionals around the world. But it is not always the best choice for beginners. Here is why it can feel overwhelming:
- It has hundreds of advanced tools and menus
- The learning curve is steep for new users
- Manual adjustments can take a long time
- It is not designed for quick, simple improvements
Photoshop is ideal for complex design projects. However, if you just want to enhance photo quality online or fix a blurry photo quickly, there are much easier options available.
Part 3. Easy Alternatives to Enhance Images Without Photoshop
Method 1: Online Photo Enhancement Tools
Online tools are quick and easy to access. You do not need to install any software. Just upload your photo, click enhance, and download the result. However, some online tools offer limited quality or restrict advanced features behind a paywall.
Method 2: Built-In Editing Features on Phones and Computers
Your phone or computer likely has basic editing tools built in. These work well for simple tasks like adjusting brightness or cropping. However, they cannot recover lost details or significantly increase image resolution.
Method 3: AI Image Enhancement Software (Recommended)
AI-powered software is the most effective option. It automatically sharpens blurry images, reduces noise, and improves color balance. You get professional-looking results without needing any editing experience.
Part 4. Improving Photos with Leawo Photo Enhancer
4.1 Introduction to Leawo Photo Enhancer
One of the best beginner-friendly options is Leawo Photo Enhancer. It is a desktop application powered by AI technology. It is designed to make image enhancement simple and fast for everyday users.
The software uses smart algorithms to upscale low-resolution photos, restore fine details, and improve overall image clarity. You can also explore Leawo PhotoIns, another tool from the same developer, which offers additional AI photo management features.
4.2 Features That Make It Beginner-Friendly
Here is what makes Leawo Photo Enhancer stand out for users without editing skills:
- AI-driven technology that handles all the technical work
- A clean and simple interface that is easy to navigate
- One-click enhancement with no manual adjustments needed
- Fast processing that saves you time
4.3 Step-by-Step Tutorial
Follow these simple steps to improve your photo quality:
- Open the Leawo Photo Enhancer software on your computer.
- Import the photo you want to improve.
- Select an enhancement mode based on your needs.
- Let the AI process the image automatically.
- Preview the result and save the enhanced photo.
Conclusion
Improving your photos no longer means spending hours in a complicated editing program. AI tools have changed the game completely. You can now enhance photo quality with just a few clicks, no experience required.
Tools like Leawo Photo Enhancer give anyone the ability to produce clearer, sharper, and more professional-looking images without any advanced editing skills. If you want better photos today, give AI-powered enhancement a try.
Technology
How Zero Trust Security Protects VPS Hosting

Virtual private servers sit in an exposed position by design. Unlike an office workstation tucked behind a corporate firewall, a VPS has a public IP address, accepts connections from anywhere in the world, and runs continuously — often without a human watching over it. That combination makes it a high-value target. Traditional security models built on perimeter defense — the idea that anything inside the network can be trusted — are no longer adequate for this threat landscape. Zero Trust is the framework that replaces that assumption entirely, and in 2026, it has become the most important shift in how VPS hosting is secured.
What Zero Trust Actually Means
Zero Trust is not a product you buy or a single tool you install. It is a security philosophy built around one core principle: never trust, always verify.
While traditional security models relied on a “castle-and-moat” approach — where the network perimeter is trusted, and access is granted based on location — Zero Trust focuses on verifying identities and device compliance regardless of location. It mandates strict identity verification and authorization for every access request, enforcing security policies based on the principle of least privilege.
Applied to VPS hosting, this means that no user, application, or service is granted access simply because it is on the same network or has connected before. Every request is treated as potentially hostile until it is verified. Continuous verification means you never inherently trust any user, device, or application, regardless of its location — inside or outside the network perimeter.
This shift matters because the old model assumed that threats come from outside. The reality is very different. Compromised credentials, malicious insiders, vulnerable applications running on the same server, and lateral movement from one breached service to another are all threats that originate from within a network. Zero Trust eliminates the blind trust that makes those attacks so damaging.
Why VPS Hosting Specifically Needs Zero Trust
A VPS is, by nature, internet-facing infrastructure. Because a VPS is highly customizable and directly exposed to the internet, it is the user’s responsibility to manage the operating system, applications, and security layers. Applying Zero Trust principles is the most effective way to manage the inherent risk of public-facing infrastructure.
The traditional approach to securing a VPS involved setting up a firewall, locking down SSH access, and keeping software updated. Those measures are still necessary, but they are no longer sufficient on their own. Modern VPS protection requires a systematic approach: from architecture to CI/CD. Standard measures like a firewall and regular updates are the baseline — but they are no longer enough.
Consider what happens when an attacker obtains valid credentials for your VPS through phishing, a data breach, or a brute-force attack. Under a traditional security model, those credentials are a skeleton key — the attacker is now “inside” and can move freely. Under Zero Trust, valid credentials alone are not enough. The request must also come from a verified device, pass behavioral checks, and be authorized for the specific resource being accessed, at that specific time.
The Core Pillars of Zero Trust for VPS Hosting
1. Identity Verification and Strong Authentication
The first line of Zero Trust defense is confirming that a user is who they claim to be — every single time they connect, not just at initial login. This means moving beyond static SSH keys and passwords toward multi-factor authentication for all administrative access.
Continuous authentication ensures that user sessions remain verified based on real-time risk assessments and not on one-time password checks. For VPS access, this translates to short-lived credentials, session tokens that expire after use, and MFA requirements that cannot be bypassed even for privileged accounts. Tools like Teleport and Cloudflare Access implement this by issuing short-lived SSH certificates rather than persistent keys — traditional SSH access relies on long-lived keys, jump hosts, and complex firewall rules, while modern zero-trust solutions eliminate these pain points by implementing identity-based access controls, short-lived certificates, and encrypted peer-to-peer connections.
2. Least-Privilege Access
Every user, application, and service running on or connecting to your VPS should have the minimum level of access needed to perform its specific function — and nothing more. This limits the blast radius of any single compromised account or process.
The default root user is all-powerful and therefore a great target. One of the most significant principles in VPS security is to reduce root usage: create a non-root user account with standard privileges immediately after initial setup, and reserve root access for operations that genuinely require it.
At the application level, this means database users who can only query the tables they need, API keys scoped to specific endpoints, and file system permissions that prevent web server processes from reading sensitive configuration files. Least-privilege access does not stop every attack, but it ensures that a breach of one component cannot immediately cascade into a full server takeover.
3. Micro-Segmentation
Micro-segmentation is one of Zero Trust’s most powerful defenses against lateral movement — the tactic attackers use to spread from one compromised service to others on the same server or network.
Micro-segmentation divides networks into small, isolated segments, each enforcing its own access controls, making it harder for attackers to pivot within the infrastructure. On a VPS running multiple services — a web application, a database, a mail server, a monitoring agent — micro-segmentation means each service communicates only with the specific other services it needs to, over defined ports and protocols. An attacker who compromises the web application cannot automatically reach the database or the mail server.
The philosophy of Zero Trust networking for VPS involves implementing micro-segmentation, applying internal firewalls to restrict traffic between your own services, and preventing an attacker from moving laterally in the event they have compromised one service. This can be implemented using iptables rules on Linux, Docker network policies, or dedicated firewall configurations that segment internal traffic just as aggressively as external traffic.
4. Continuous Monitoring and Anomaly Detection
Zero Trust does not assume that a verified session remains trustworthy for its entire duration. The security posture of users and devices is continuously monitored for anomalies and potential threats. Sensitive resources are isolated into smaller, protected segments to limit the spread of a potential breach.
For VPS hosting, continuous monitoring means watching for unusual patterns: a login from an unfamiliar geographic location, a user account suddenly accessing files it has never touched before, an outbound connection to an unknown IP, or a process consuming unexpected CPU resources. Tools like Fail2Ban, OSSEC, and auditd provide this visibility at the server level. Modern VPS protection using a Zero Trust stack incorporates AI-driven intrusion detection and prevention systems that can detect anomalies in real time, isolate processes, and even automatically restore configuration after an attack.
The goal is to reduce dwell time — the period between when an attacker gains access and when they are detected. The average dwell time in breaches without continuous monitoring is measured in weeks. With Zero Trust monitoring in place, anomalies are surfaced within minutes or hours.
5. End-to-End Encryption
Zero Trust assumes that any network, including your own internal network, could be compromised. Therefore, all traffic — not just traffic crossing the public internet — must be encrypted.
Zero Trust solutions mandate end-to-end encryption for all connections, both at rest and in transit. This ensures that sensitive data remains protected from eavesdropping or interception, even on unsecured networks. Encryption standards such as TLS and IPsec are enforced across all channels, with regular updates to protocols and keys to address evolving threats.
For a VPS environment, this means enforcing HTTPS for all web traffic, encrypting database connections even when the database is on the same server, encrypting data at rest on disk, and using encrypted tunnels like WireGuard for administrative access. WireGuard, together with SASE providers such as Tailscale or Cloudflare One solves several tasks at once: access to the server is strictly controlled, all traffic is encrypted, and geography does not matter — whether it is an office in one country or a remote worker in another.
6. Just-in-Time Access and Minimal Exposure
One of the most effective Zero Trust tactics for VPS security is making your server invisible by default. Rather than leaving SSH open on port 22 permanently — waiting for brute-force attempts — you only expose access when it is actively needed.
Applications and workloads are not reachable by default and only become accessible after strict validation. Techniques like just-in-time access and one-time, ephemeral connectivity further restrict potential attack vectors. Services like Cloudflare Access and Teleport implement this natively. Without them, you can approximate it by closing all administrative ports in your firewall by default and opening them only via an authenticated knock sequence or a VPN connection.
Port scanners are constantly sweeping the internet looking for exposed SSH, RDP, and admin panel ports. A server that does not expose these ports by default simply does not appear in those scans.
Implementing Zero Trust on Your VPS: Practical Starting Points
You do not need an enterprise security budget to begin applying Zero Trust principles to your VPS. Here is a practical sequence to follow:
- Start with authentication. Disable password-based SSH login and switch to key-based authentication. Add MFA for any control panel or admin interface. Consider deploying Tailscale or Cloudflare Access to gate SSH access behind identity verification.
- Apply least privilege immediately. Create non-root users for all services. Audit every running process and ask whether it needs its current level of access. Revoke anything that doesn’t.
- Segment your services. Use your firewall to block inter-service traffic that does not need to happen. Your web server should not be able to initiate connections to your database on its own — only respond to requests from your application layer.
- Enable logging and monitoring. Deploy auditd, Fail2Ban, or an equivalent to watch for suspicious activity. Set up alerting so that anomalies reach you in real time rather than sitting in a log file you check monthly.
- Encrypt everything. Enable full-disk encryption on your VPS storage, enforce TLS on all services, and audit your server for any service transmitting data in plaintext.
The Bottom Line
For a VPS that is constantly exposed to the internet, regular auditing transforms passive security into an active defense strategy. Instead of waiting for a breach, Zero Trust proactively identifies misconfigurations, outdated software, and excessive permissions before they become vulnerabilities.
The old perimeter defense model assumed the threat was outside. Zero Trust acknowledges that the threat can already be inside — through a stolen credential, a vulnerable plugin, a misconfigured service, or a compromised dependency. By verifying every request, restricting every permission, segmenting every service, encrypting every connection, and monitoring every session, Zero Trust turns your VPS from a single point of failure into a layered system where compromising one component does not hand an attacker the entire server. That shift in assumption is what makes it the defining security framework for VPS hosting in 2026.
Technology
How the charging station and magsafe charger are changing the future of smart charging

Technology has become an essential part of everyday life. Smartphones, smartwatches, wireless earbuds, and tablets are now used constantly for work, entertainment, and communication. As the number of devices increases, people are searching for faster and more convenient ways to keep everything powered. This is where the charging station and the magsafe charger are making a major difference.
Modern users no longer want messy cables spread across desks and bedside tables. They prefer organized and efficient charging solutions that save time and space. The rise of wireless technology has made charging more comfortable, and both the charging station and the magsafe charger are leading this transformation.
What is a charging station
A charging station is a device designed to charge multiple electronic products at the same time. Instead of using separate chargers for every gadget, users can connect everything in one organized location.
The popularity of the charging station has increased because it reduces clutter and simplifies daily routines. Many models now support smartphones, tablets, smartwatches, and wireless earbuds all together.
When combined with a magsafe charger, the charging experience becomes even more efficient. Wireless magnetic alignment makes charging faster and more reliable for compatible devices.
Understanding the magsafe charger
The magsafe charger is a magnetic wireless charging system designed to attach securely to compatible smartphones and accessories. It uses magnets to align the charger perfectly with the device, ensuring stable and efficient power transfer.
One of the biggest advantages of the magsafe charger is convenience. Users no longer need to struggle with plugging in cables, especially during busy moments or at night.
Many modern charging station products now include built-in support for the magsafe charger, allowing users to power multiple devices while maintaining a clean setup.
How charging station and magsafe charger work together
The combination of a charging station and a magsafe charger creates a complete charging solution for modern lifestyles. A user can place their smartphone on the magnetic charging area while charging other devices at the same time.
This setup improves organization and saves space, especially in homes and offices where multiple devices are used daily. The charging station keeps everything in one place, while the magsafe charger provides wireless convenience.
Another benefit is efficiency. Since the magsafe charger automatically aligns with the phone, users receive consistent charging performance without constantly adjusting cables.
Benefits of using these technologies
One of the biggest advantages of a charging station is convenience. Instead of managing several chargers, users can organize all their devices in one central location.
The magsafe charger also improves the user experience by making wireless charging easier and more reliable. Magnetic alignment reduces charging interruptions caused by incorrect placement.
Another major benefit is portability. Many modern charging station models are compact and travel-friendly. Combined with a magsafe charger, they provide a practical solution for people who travel frequently.
Applications in daily life
The use of a charging station has become common in homes, offices, and public spaces. Families often use one central charging area to keep devices organized and fully powered.
The magsafe charger is especially popular among smartphone users who prefer wireless technology. It allows quick charging during work, study sessions, or even while relaxing at home.
Businesses are also adopting the charging station concept in waiting rooms, hotels, and airports. Adding a magsafe charger gives customers a more modern and comfortable experience.

Challenges and limitations
The magsafe charger also works best with compatible devices. Users with older smartphones may not experience the same magnetic functionality.
Another challenge is charging speed. While wireless charging is convenient, some users still believe wired charging can provide faster results compared to a magsafe charger.
The role of innovation in charging technology
Innovation continues to improve both the charging station and the magsafe charger. Manufacturers are creating more efficient systems with faster charging speeds and better energy management.
New versions of the charging station are being designed with sleek styles and smart features, making them suitable for modern workspaces and homes.
At the same time, the magsafe charger is evolving with stronger magnets and improved wireless technology, providing better performance and user comfort.
The future of smart charging
The future of the charging station looks promising as wireless technology becomes more common. Experts expect charging systems to become smaller, faster, and more energy efficient.
The magsafe charger will likely continue expanding into other devices beyond smartphones, including tablets, accessories, and wearable technology.
Together, the charging station and the magsafe charger represent the future of organized and intelligent charging solutions for modern lifestyles.
Conclusion
The rise of the charging station and the magsafe charger has transformed how people power their devices. These technologies provide convenience, organization, and a cleaner charging experience.
While there are still some limitations, the benefits are clear. A charging station simplifies device management, while the magsafe charger adds wireless comfort and reliability.
As innovation continues, both the charging station and the magsafe charger will become even more advanced, helping users stay connected in a faster and more efficient digital world.
Technology
How iTop Voicy Makes Real-Time Voice Changing Simple and Fun

The modern online world relies on conversation. Gamers coordinate strategies through voice chat, streamers entertain live audiences for hours, and content creators constantly look for new ways to keep viewers engaged. In all these areas, audio is as important as visuals.
Yet many people hesitate to use voice-changing software. They worry about complex controls, delayed audio, or unnatural sound effects. This hesitation is understandable. A tool that disrupts communication instead of improving it quickly becomes frustrating.
iTop Voicy takes a different approach. Its strength lies not only in the variety of voice effects but also in how it makes real-time voice changing feel natural, smooth, and enjoyable from the start.
When Communication Becomes Part of the Experience
Live interaction has transformed digital entertainment. A funny reaction during a game, a dramatic moment in a livestream, or a creative character voice during a group chat can make an experience instantly more memorable.
This is where iTop Voicy proves useful. Instead of requiring users to edit audio afterward, the software changes voices instantly while speaking. A player can surprise teammates with a deep cinematic voice during a match. A streamer can use a humorous effect to entertain viewers. A creator recording short videos can add personality without spending extra hours on audio production.
The result feels immediate and authentic because reactions happen in real time.
Designed for People Who Want Simplicity
One reason many users avoid voice changers is the fear of technical setup. Some programs need advanced sound configuration or external audio tools to function properly.
iTop Voicy eliminates much of that complexity. The interface is straightforward, allowing beginners to experiment confidently without feeling overwhelmed. Voice effects are organized clearly, and switching between them takes only a few clicks.
That simplicity matters more than it might seem. During a live stream or online game, no one wants to pause to solve audio issues. Users need a voice changer that works quietly in the background while they focus on communication and content creation.
More Than Just Funny Sound Effects
While entertainment is a major reason people use a voice changer, the appeal of iTop Voicy goes beyond jokes and pranks. Many creators use voice customization as part of their online identity.
Some streamers develop recurring characters with unique voices. Others make subtle sound adjustments to enhance their commentary. Even remote teams and online communities sometimes use voice effects to create a lighter, more interactive atmosphere during long conversations.
iTop Voicy works with platforms like Discord, Twitch, Zoom, OBS, and online games, fitting naturally into different digital environments. Users do not need separate tools for every platform they use.
How to Use iTop Voicy
1. Download and install iTop Voicy on your computer.
2. Connect your microphone and launch the software.
3. Browse the available voice filters and choose one that fits your style or situation.
4. Set iTop Voicy as your microphone input in your gaming, streaming, or communication platform.
5. Test the voice effect in real time and adjust settings if necessary.
6. Start chatting, gaming, or streaming with your selected voice effect active.
A Smarter Way to Make Online Interaction Memorable
Digital communication has become more expressive than ever. People no longer want conversations that feel flat or predictable, especially in gaming and streaming environments where personality shapes the entire experience.
iTop Voicy succeeds because it recognizes that voice changing should feel effortless, not technical. It provides users with a simple way to add creativity, humor, and individuality to real-time conversations without interrupting the flow of interaction.
For creators, gamers, and anyone who spends time communicating online, this balance of simplicity and entertainment makes iTop Voicy a tool worth exploring.
-

 Celebrity3 months ago
Celebrity3 months agoAll About Jazmyn Bieber: The Justin Bieber’s Little Sister’s
-

 Celebrity3 months ago
Celebrity3 months agoWho Is Peter Hernandez? The Real Story of Bruno Mars’ Father
-

 Biographies2 months ago
Biographies2 months agoWho Is Daniel Mara? The Untold Story of Kate Mara’s Private Sibling
-

 Biographies3 months ago
Biographies3 months agoWho Is Shameera? All You Need To Know About Charli XCX’s Mother
-

 Biographies3 months ago
Biographies3 months agoWho is Todd McRae? Meet Tate McRae’s Father
-

 Biographies3 months ago
Biographies3 months agoMeet Rosemary Turner: The Mother of Actor Callum Turner
-
 Biographies3 months ago
Biographies3 months agoWho Is Alvin Martin? All About the Whoopi Goldberg’s First Husband
-

 Celebrity3 months ago
Celebrity3 months agoWho Is Monica Turner? All About the Life of Mike Tyson’s Former Wife



